How to Protect Your Mobile Applications from Common Threats
The Importance of Understanding Vulnerabilities in Mobile Applications
In today’s digital landscape, mobile applications have become indispensable tools in our everyday lives. They facilitate various aspects of our daily routines—from communicating with friends and family to managing finances and navigating our day-to-day tasks. As these applications continue to surge in popularity, the threats they face only grow more daunting. An increasing number of vulnerabilities threaten both user data and the integrity of these applications. Thus, it is crucial for both developers and users to recognize and combat the common threats faced by mobile applications.
Common Security Threats
To effectively safeguard applications, it is vital to identify specific security issues that can compromise their safety. Some of the most pressing threats include:
- Malware: Malicious software can infiltrate devices, stealing personal information such as passwords, financial data, and even private messages. For instance, trojan malware disguises itself as a legitimate application, tricking users into unwittingly sharing sensitive information.
- Data Interception: Information transmitted over networks can be intercepted by cybercriminals. This vulnerability is particularly pronounced in public Wi-Fi networks, where unencrypted data can easily be accessed. For example, a hacker could intercept login credentials as they are transmitted between a user’s device and a mobile application.
- Unsecured APIs: Weak application programming interfaces (APIs) can act as gateways for attackers, exposing sensitive data and functionality. A notable case involves social media platforms where poorly secured APIs allowed attackers to access user data and conduct unauthorized actions.
Alarming Statistics and the Need for Security
The statistics regarding mobile application security are alarming. Recent studies indicate that nearly 60% of mobile applications lack basic security features, underscoring the critical need for enhanced security measures. This negligence places vast amounts of personal and financial information at risk, leading to mounting concerns among users. Developers must recognize that their responsibility extends beyond merely creating functional applications; they must prioritize building robust defenses against potential cyber threats.
Strategies for Strengthening Application Security
In this article, we will delve into effective strategies to fortify your mobile applications by discussing the latest security protocols and best practices that minimize risks. From using encryption to protect data transmission to regularly updating applications to patch vulnerabilities, the options for increasing security are manifold. As the mobile landscape evolves, so must the strategies employed to protect sensitive data and offer users a secure experience.
By equipping themselves with the right knowledge and tools, developers can create a secure mobile experience, fostering user trust and ensuring the longevity of their applications. As we explore the complexities of app protection, this will empower readers to take an active role in safeguarding their digital interactions.
DISCOVER MORE: Click here to learn how automation tools can revolutionize your workflow
Effective Defense Mechanisms Against Mobile Application Threats
Understanding the myriad of threats mobile applications face is just the first step; implementing practical solutions is where the real challenge lies. As developers and users alike confront a rapidly evolving cyber landscape, embracing robust security practices becomes essential. Here we explore the key strategies designed to bolster mobile application security and mitigate the risks associated with malware, data interception, and unsecured APIs.
1. Employ Strong Encryption Techniques
Encryption acts as a formidable shield against data breaches and unauthorized access. By encoding sensitive data, developers can ensure that even if malicious actors intercept this information, it remains unreadable without the proper decryption keys. Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols are pivotal in encrypting data during transmission over networks. For instance, utilizing HTTPS instead of HTTP for data exchange not only secures the transmission but also instills greater user confidence in the application’s safety.
2. Regularly Update and Patch Applications
One of the simplest yet most effective methods to protect your mobile app is by implementing a structured plan for regular updates and patching vulnerabilities. Cyber threats evolve, and so should the defenses of your application. It’s vital for developers to monitor for updates in libraries, frameworks, and plugins regularly used in their mobile apps. Each new version often includes essential security patches that can mitigate previously identified vulnerabilities. Statistics reveal that around 90% of security breaches occur due to unpatched software; thus, timely updates can significantly reduce the chances of exploitation.
3. Validate Input and Secure APIs
Weaknesses in APIs can render an application susceptible to threats like data exposure and unauthorized access. Developers should prioritize input validation to ensure that only expected and safe data is processed. This practice not only prevents various forms of injection attacks but also enforces consistency in the data being handled. For instance, limiting API access by implementing proper authentication methods (such as OAuth 2.0) and defining roles for users can help secure sensitive endpoints and data.
4. Employ a Comprehensive Testing Strategy
Regular testing of mobile applications should not be an afterthought; instead, it must be an integral part of the development lifecycle. Conducting thorough penetration testing and vulnerability assessments can unveil hidden weaknesses before an attacker exploits them. Automated testing tools can also enable continuous assessment and ensure that security measures are in place throughout the app’s evolution. According to industry experts, 75% of security issues can be identified through rigorous testing, enhancing an app’s resilience and trustworthiness.
5. Educate Users on Best Practices
While developers carry the responsibility of building secure applications, users also play a vital role in maintaining cybersecurity hygiene. Educating users about best practices, such as downloading apps only from official sources, enabling two-factor authentication, and recognizing phishing attempts, can significantly reduce the risk of security breaches. Developers should provide users with clear, informative guides that empower them to take proactive steps towards safeguarding their own data.
By combining these strategies, developers can fortify mobile applications against common threats while fostering a safer digital experience for all users. The journey towards enhanced app security is ongoing, and continuous commitment to learning and adapting to new cyber threats is essential.
In today’s digital landscape, mobile applications face a myriad of threats that can compromise user data and software integrity. Understanding how to defend against these vulnerabilities is crucial for developers and businesses alike. This section delves into the specific challenges and protective measures to secure mobile applications from common risks like malware, data breaches, and insecure coding practices.
Understanding Common Mobile Application Threats
Common threats to mobile applications include malware, which can infiltrate devices through malicious app downloads, and data breaches, where unauthorized access to sensitive information occurs. Developers must be vigilant about these issues as they represent significant risks to both users’ privacy and the reputation of the app.
Adopting Secure Coding Practices
One effective strategy for protecting mobile applications is through the implementation of secure coding practices. This ensures that the code is free from vulnerabilities that could be exploited by cybercriminals. Common secure coding guidelines include validating user input, employing proper authentication mechanisms, and regularly updating libraries to patch known security holes.
Regular Security Audits and Testing
Conducting security audits and penetration testing regularly can help identify weak points in mobile applications. By simulating attacks, developers can uncover potential vulnerabilities and rectify them before they can be exploited in the real world. Additionally, automated tools and frameworks can assist in maintaining rigorous security checks throughout the development lifecycle.
User Education and Awareness
Finally, educating users about the risks associated with mobile applications and how to recognize potential threats is paramount. Promoting secure download practices and providing guidance on safeguarding personal information can greatly reduce the risk of compromise. Users should also be advised to regularly update their apps and operating systems to protect against new vulnerabilities.
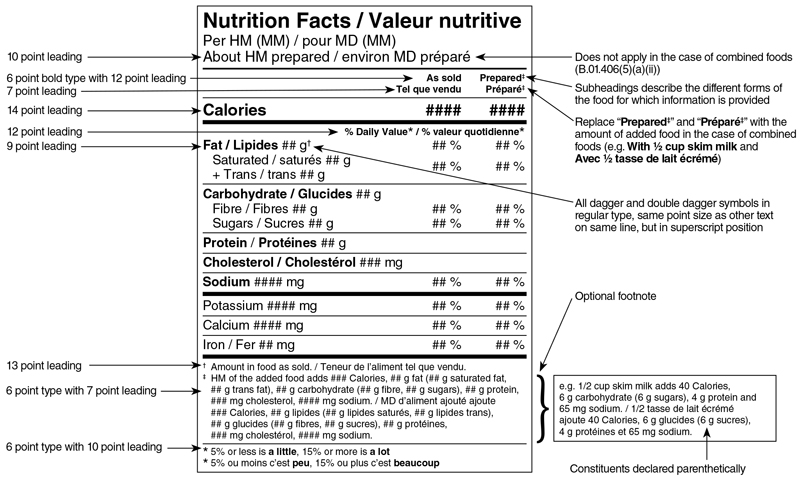
| Category 1 | Category 2 |
|---|---|
| Malware Protection | Adopting anti-malware solutions for app integrity. |
| Data Encryption | Encrypting sensitive data to prevent unauthorized access. |
By understanding the threats mobile applications face and employing these strategies, developers can significantly enhance their protective measures. From coding practices to user education, each layer of defense is critical in creating a secure mobile environment. Stay tuned for more insights into advanced protection techniques and tools that can further fortify your mobile applications.
DISCOVER MORE: Click here to boost your focus
Enhancing Security through User Trust and Technological Innovation
As the digital landscape continues to evolve, protecting mobile applications from common threats requires a balanced approach that incorporates both user trust and technological innovation. With threats becoming increasingly sophisticated, it’s imperative to explore additional strategies that not only reinforce app security but also enhance user experience and confidence.
6. Implement Multi-Factor Authentication (MFA)
The integration of Multi-Factor Authentication (MFA) is a powerful method for safeguarding mobile applications against unauthorized access. By requiring users to verify their identity through multiple methods—such as a password coupled with a verification code sent via SMS or email—developers can fortify applications against credential theft. Research indicates that MFA can prevent up to 99.9% of account compromise attacks, underscoring its importance in a comprehensive security strategy.
7. Monitor App Behavior with Anomaly Detection
Employing anomaly detection algorithms to monitor application behavior can act as an early warning system for potential security threats. By analyzing user interactions and system patterns, developers can swiftly identify unusual activities that may signify a data breach or other malicious actions. For instance, a sudden spike in data requests or logins from unfamiliar locations can trigger alerts for further investigation, allowing teams to mitigate threats in real-time. This proactive approach not only enhances security but also improves user trust in the app.
8. Secure Mobile Payment Processes
With the rise of mobile commerce, securing payment processes has become a critical aspect of mobile application security. Developers should integrate secure payment gateways that use transaction encryption to protect sensitive financial data. Leveraging technologies such as tokenization can also reduce the risk associated with storing credit card information. By replacing actual card details with a unique identifier or token, developers can ensure that even if data breaches occur, sensitive information remains protected.
9. Utilize Threat Intelligence and Security Analytics
Engaging in threat intelligence can significantly enhance the security posture of mobile applications. By staying informed about emerging threats and vulnerabilities, developers can adapt their security measures in a timely manner. Additionally, leveraging security analytics can provide valuable insights into existing risks and potential weaknesses within an application. According to recent studies, organizations using threat intelligence to guide security decisions were able to reduce the average time to detect breaches by 45%, enhancing their responsiveness to incidents.
10. Focus on Comprehensive App Awareness
In a world where mobile applications are central to daily activities, fostering awareness around application security among users is paramount. Developers should employ in-app prompts that educate users about privacy settings, share tips for safeguarding their devices, and remind them about the importance of updating app versions frequently. By creating a culture of security awareness, users become active participants in securing their data, ultimately reducing the overall vulnerability of the application. Regularly updated FAQs or blogs can further serve as resources for users seeking additional information.
Through the adoption of these advanced security measures and the cultivation of user awareness, mobile applications can not only protect their critical data but also build a relationship of trust with their users. As threats grow more complex, the emphasis on innovation and responsiveness will play a crucial role in shaping the future of secure mobile applications.
DISCOVER MORE: Click here for more insights
Conclusion: Cultivating a Resilient Mobile Application Ecosystem
As we move deeper into the age of mobile technology, securing applications is not just a technical requirement, but a vital component of user satisfaction and trust. The myriad of threats facing mobile applications—from data breaches to identity theft—necessitates a proactive and multifaceted approach to security. By implementing best practices such as Multi-Factor Authentication (MFA), anomaly detection, and secure payment processes, developers can significantly enhance the resilience of their applications. Furthermore, leveraging threat intelligence and security analytics can help identify vulnerabilities before they are exploited, thereby mitigating risks more effectively.
Crucially, fostering user awareness around security must be prioritized. Educating users about their role in protecting their personal data, combined with creating a culture of vigilance, not only empowers them but also supports the strengthening of the application’s defenses. This shared responsibility between developers and users can lead to a more secure ecosystem.
In conclusion, as the landscape of cyber threats continues to evolve, so too must our strategies to combat them. Emphasizing innovation, user trust, and comprehensive security measures will not only protect mobile applications from current threats but will also prepare them for future challenges. By embracing these practices, both developers and users can ensure a safer digital environment for all, ultimately shaping the future of mobile application security.