How to Identify and Avoid Malicious Apps on Your Device

Understanding the Landscape of Malicious Apps
In our increasingly interconnected world, where nearly 85% of American adults own a smartphone, malicious apps pose a daunting threat to digital privacy and security. These rogue applications can easily infiltrate devices, often masquerading as harmless tools promising productivity, entertainment, or convenience. Recognizing the subtle indicators of potentially harmful software is critical for safeguarding your personal data and digital footprint.
The risks grow multifold when users lack awareness of how these apps operate. Many applications may exhibit strange behavior, such as excessive battery drain or unexplained data usage. For instance, a photo editing app that suddenly starts accessing your contacts list may be raising a significant red flag. Additionally, social engineering tactics play a substantial role in duping users. Attractive designs and appealing reviews can entice individuals to download, leading them into a trap. A classic example is scam apps that promise to enhance device performance but instead serve to harvest personal information.
Equally alarming is the phenomenon of permission overreach. Oftentimes, users blindly accept app permissions, which can include access to sensitive information like location, contacts, and even camera functionality. A navigation app might legitimately request location access, while a simple game should not require such extensive permissions. Therefore, becoming vigilant about installed apps is essential.
Strategies for Identifying Safe Apps
To diminish the risk of downloading malicious software, several strategies can be adopted:
- Research the developer: Conduct a background check on the app’s developer. Renowned developers typically have substantial reputations and multiple credible applications in the market. A quick online search can reveal much about their history and reliability.
- Read user reviews: Delve into user feedback and ratings. Patterns in reviews can often expose consistent issues, particularly concerning security concerns. Look for reports of suspicious behavior or poor support from the developer.
- Check permissions: Before finalizing installation, take a moment to carefully review the permissions requested. Ensure they are relevant to the app’s features; a music app should not require access to your camera or contacts.
By employing these strategies diligently, you can greatly reduce the likelihood of downloading malicious apps that could compromise your personal information or device integrity. As the app landscape continues to evolve, remaining informed and cautious is the best defense against digital threats. Throughout this article, we will explore additional proactive measures and offer further insights to help you navigate app stores with confidence, ensuring your digital safety in a rapidly changing environment.
DISCOVER MORE: Click here to deepen your understanding
Recognizing the Indicators of Malicious Apps
As technology continues to advance, users must equip themselves with the knowledge necessary to navigate the sometimes murky waters of app stores. With a staggering 1.5 million apps available on major platforms like the Google Play Store and Apple App Store, selecting safe and trustworthy applications can feel like finding a needle in a haystack. Understanding the key characteristics of malicious apps is critical to ensuring a secure mobile experience and protecting personal data.
Many malicious applications exhibit specific warning signs that can alert users to potential dangers. For instance, excessive resource consumption is a common indicator of a nefarious app. Applications that lead to significant battery drain, unusually high data usage, or unexpected crashes may be up to no good. If your high-quality photo editing app starts malfunctioning and demanding more processing power than anticipated, it’s time to investigate further. Regularly monitoring your device’s performance can significantly aid in spotting these issues.
Unusual behavior is another tell-tale sign of a malicious app. For example, if a simple gaming app suddenly attempts to access your microphone or location data, alarm bells should ring. Legitimate applications should only request the permissions necessary for their functions. A messaging app shouldn’t need your location, and a trivia game should not require access to your contacts. Always be cautious about apps that behave outside their intended functionality, as these anomalies are often a red flag.
Common Characteristics of Malicious Apps
By familiarizing yourself with the common traits of malicious apps, you can better protect yourself and your device. Here are some characteristics to watch for:
- Deceptive App Store Listings: Beware of apps with poorly written descriptions, spelling errors, or generic imagery that fail to convey legitimacy.
- Unusually High Permissions: Assess permission requests critically; suspicious apps often request more access than they legitimately need.
- Low-Quality User Ratings: Analyze user ratings and reviews; significant numbers of one-star ratings or complaints regarding privacy breaches should raise a red flag.
- Frequent Updates with Unclear Changes: Be cautious of apps that have frequent updates with vague notes about improvements. This behavior could indicate ongoing malicious activities.
Recognizing these characteristics can empower users to make informed decisions when downloading applications. The app market is rife with potential threats, and being aware of how malicious apps present themselves is vital to your digital health and security. The next step involves going beyond merely identifying these risks; you must also understand how to mitigate them effectively. As this article continues, we will delve into essential tools and techniques that can further enhance your app safety strategies, equipping you with the confidence needed to explore the vast world of apps without fear.
How to Identify and Avoid Malicious Apps on Your Device
In today’s digital landscape, where the vast expanse of applications is at our fingertips, learning how to protect your device from malicious apps is paramount. Malicious applications can not only compromise your personal data but also disrupt your device’s functionality. Understanding how to identify and avoid these apps is the first step towards securing your online life.
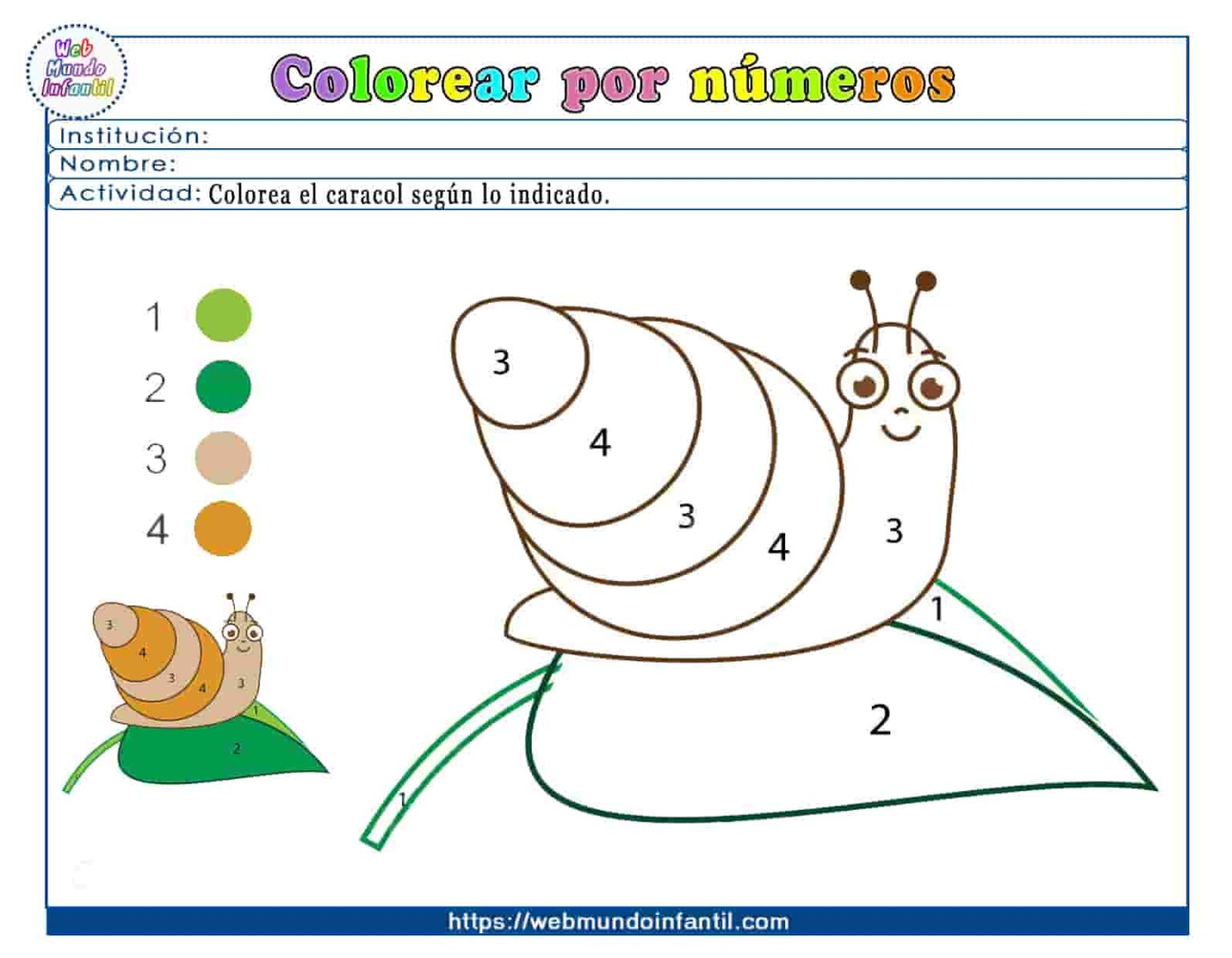
| Detection Method | Sign of Malicious Apps |
|---|---|
| Permissions Review | Unrequested access to sensitive information like contacts or location |
| User Ratings | Low user ratings or numerous complaints about suspicious activity |
One effective way to protect yourself is by paying close attention to app permissions. If an app requests access to more information than necessary, it may be a red flag. Following this, examining user reviews is crucial; a lack of positive feedback or frequent warnings from users can indicate that an app may not be trustworthy. Armed with this knowledge, you can make informed decisions and safeguard your valuable information.
Furthermore, consider installing a reputable antivirus or mobile security application. These tools can scan for malicious behavior, adding another layer of security to your device. Always ensure that your operating system and apps are up-to-date, as updates often contain important security patches.
Incorporating these strategies will greatly reduce your risk of downloading harmful applications. Stay vigilant and informed to keep your device secure from threats in the vast app marketplace.
LEARN MORE: Click here to understand why app privacy policies matter
Essential Tools and Techniques for App Safety
Beyond recognizing the indicators of malicious apps, employing practical tools and techniques is pivotal to maintaining a secure mobile environment. Understanding the options available can transform a user from a passive consumer of technology into an empowered protector of their devices and personal information.
First and foremost, leveraging antivirus and security apps can significantly bolster your defense against malicious applications. Numerous reputable security companies offer dedicated mobile security applications that scan for malware, unsafe apps, and vulnerabilities. These tools not only help identify potential threats but also provide real-time protection against harmful downloads and updates. For example, options like McAfee Mobile Security or Avast Mobile Security provide robust scanning features that can help detect apps that may compromise your device’s security.
Regular Software Updates
Staying current with software updates is another crucial practice to ensure device security. Developers promptly address vulnerabilities by releasing updates that often include critical security patches. Failing to update your device or neglecting app updates can leave you exposed to malicious exploits. Ensuring automatic updates are enabled can reduce the hassle of manually checking and keep your device protected from known threats.
Monitoring App Behavior
Utilizing your device’s built-in settings to monitor app behavior can also provide valuable insights into potential vulnerabilities. For instance, both Android and iOS platforms offer detailed information on app permissions and data usage. Regularly reviewing which apps have access to sensitive information can help users identify questionable applications. If an app is using excessive data or resources without a clear reason, it may be time to uninstall it.
Using Reputable Sources for App Downloads
Always prioritize downloading applications from legitimate sources. Although third-party stores may boast an extensive selection of apps, they often lack the rigorous vetting processes of the official app marketplaces. Even in legitimate app stores, utilize the search function judiciously, and avoid clicking on advertisements that lead to suspicious listings. An app that appears prominently advertised may not necessarily be safe. Stick with well-known applications and familiarize yourself with various developers to enhance your chances of making safe choices.
Educate Yourself on Privacy Policies
Before downloading an app, consider reviewing its privacy policy. While many users overlook this step, understanding how your data will be used, stored, and shared is vital. Legitimate apps typically have clear and concise privacy policies that inform users of their practices. A lack of sufficient transparency in a privacy policy, or an overly complex document filled with legal jargon, could be indicative of darker practices lurking beneath the surface.
Uninstalling Apps That Raise Red Flags
If you identify an app showing signs of malicious intent, it’s vital to take immediate action. Uninstalling the app may not be sufficient; clearing its data and cache, as well as checking for any unusual permissions it may have requested, ensures your device remains safe. Many skilled malicious apps may leave remnants behind that can continue to jeopardize your security.
By integrating these tools and techniques into your daily digital practices, you can effectively fortify your defense against malicious apps. Building a foundation for lifelong security starts with informed decisions and a proactive approach to app management. As you adopt these safety strategies, remember that vigilance is key in the ever-evolving landscape of mobile threats.
DISCOVER MORE: Click here to enhance your prototyping skills
Conclusion: Safeguarding Your Digital Life
In our increasingly interconnected world, the importance of identifying and avoiding malicious apps cannot be overstated. Armed with the knowledge and tools discussed, you now have the power to protect your devices and sensitive information from potential threats. Recognizing the red flags of malicious applications is just the beginning; implementing a comprehensive approach to app management is essential for maintaining your digital safety.
By utilizing antivirus and security apps, ensuring regular software updates, and monitoring app behavior, you are taking crucial steps toward safeguarding your online presence. Additionally, downloading from reputable sources and understanding app privacy policies serve as fundamental components in the fight against cyber threats. These practices not only protect your device but empower you as a user to make informed decisions.
Furthermore, staying vigilant and proactive is key in an environment where malicious techniques continue to evolve. Regularly reassessing your apps and being alert to signs of suspicious activity will enhance your security posture. Remember, the digital landscape is full of potential pitfalls, but with these strategies, you can navigate safely and confidently.
As technology continues to advance, so too does the need for heightened awareness and adaptability in combating threats. Embrace this knowledge as a skill set that grows over time, allowing you to enjoy the benefits of technology while keeping your personal information secure. The journey to digital safety is continuous, and your commitment to diligence will serve as your best defense against malicious apps.