App Permission Management: What You Need to Know to Keep Your Devices Secure
Understanding App Permissions for Enhanced Security
In the fast-paced world of technology, the applications we use daily can access a multitude of sensitive data on our devices. This raises serious concerns about privacy and security. App permissions act as the gatekeepers, determining what information apps can access and how they can interact with your device’s hardware and software. From social media to dating apps, understanding how to manage these permissions is essential for protecting your personal information in an increasingly digital society.
Granular Control
When you install an application, it often requests a variety of permissions, ranging from access to your camera to the ability to track your location. It is crucial for users to know what permissions are being requested and why. For instance, a photo editing app may need access to your camera and photo library, which is justifiable. However, if a simple flashlight app requests access to your contacts, that raises a red flag. Users should always scrutinize these requests, and only grant permissions that align with the app’s core functionality.
Common Permissions
Some of the most commonly requested permissions include:
- Camera Access: Used by photography or video communication apps for capturing pictures and streaming video.
- Microphone Access: Essential for voice messaging or audio recording apps but can also invade privacy if misused.
- Location Access: Often requested by navigation and food delivery apps, but it can track your movements more than necessary.
- Contacts Access: Needed by messaging apps to facilitate communication, yet it can expose personal information to unwanted entities.
Privacy Risks
Granting excessive permissions can lead to significant privacy risks. For example, a malicious app could collect and transmit your data to third parties without your consent, resulting in unauthorized data sharing or personal information leaks. In recent years, several high-profile data breaches have occurred where users’ private information was compromised due to improper management of app permissions. These incidents underscore the importance of being vigilant and proactive about which apps you’re allowing into your personal digital space.
As the number of apps continues to rise, staying informed about permissions best practices becomes not just wise, but essential. Cybersecurity threats are evolving rapidly, and with them, so are the tactics employed by malicious apps. Understanding app permissions is a crucial step in protecting your privacy and identity in an increasingly connected world.
Are you empowered enough to navigate your permission settings? Familiarizing yourself with permission management strategies can significantly enhance your digital security and privacy. In this article, we will delve deeper into effective app permission management techniques that can help you safeguard your data in the digital age.
LEARN MORE: Click here to discover essential security settings
Essential Strategies for Managing App Permissions
In a world where our smartphones and tablets are an extension of ourselves, the applications we install often ask for a level of access that can be surprising. With each tap on the “Install” button, users are faced with a multitude of app permission requests, and understanding the implications of these permissions is key to maintaining digital security. Knowing how to manage these permissions not only protects sensitive information but also preserves the integrity of your device.
Evaluating Permission Requests
When an app requests permission, it often accompanies a justification; however, these explanations can be vague or misleading. To avoid falling into a trap, users should perform a thorough evaluation of permission requests. Ask yourself the following questions:
- Is this permission necessary for the app’s primary function? A note-taking app, for instance, foresees a need for accessing your storage, but does a weather app require this access?
- What alternatives exist? Many apps can perform their functions without accessing extensive personal data. Research may unveil alternative solutions that respect your privacy.
- How reputable is the app developer? A well-known and trusted developer is more likely to adhere to ethical standards in handling user data. Always check the developer’s credentials and reviews before granting permissions.
Limiting Access Post-Installation
Once you’ve granted permissions, it’s easy to forget about them. However, it’s essential to periodically review and manage these permissions to align with your current usage. Most operating systems allow you to change app permissions post-installation. Consider conducting a routine check to revoke permissions for apps that no longer serve a purpose, particularly those that store sensitive data such as health information or financial details.
Permissions and Updates
App updates are another critical consideration when it comes to app permission management. Developers frequently release updates to improve functionality or patch security vulnerabilities, but these updates can also introduce new permission requests. Users may unknowingly allow increased access to apps without understanding the added risks. Thus, it is vital to read through the change logs provided during updates to stay informed about what new permissions are being sought.
As app developers iterate and integrate new features, there’s a growing potential for permissions creep, where apps gradually request more access over time. This creeping tendency highlights the need for users to be vigilant and proactive about their choices. By consistently managing permissions, you create a more secure digital space that protects your most personal information.
With advancements in technology and an ever-growing app ecosystem, mastering app permission management is no longer optional—it’s a necessity. In the following sections, we will explore more specific techniques and tools you can use to navigate the complex landscape of app permissions effectively.
When it comes to App Permission Management, understanding the intricacies of how apps interact with your device and personal information is crucial for maintaining your security. Mobile applications often request various permissions upon installation that, while they can enhance functionality, may also pose significant privacy risks if not managed properly.One key aspect of permission management is discerning which permissions are essential for the app’s performance versus those that are not. For example, a simple note-taking app requesting access to your contacts or location raises red flags. Users should critically assess these requests and be cautious when granting permissions that don’t align with the primary function of the application.Moreover, many devices now feature built-in tools that allow users to review and adjust app permissions at any time. This proactive approach can help mitigate risks such as data leakage or intrusive advertising practices. By regularly auditing app permissions, users can ensure that they maintain control over their sensitive information.Another consideration is that developers must offer transparency regarding the data collected and how it is used. Well-informed users equip themselves with the knowledge required to discern trustworthy apps from potentially harmful ones. Therefore, researching app backgrounds and reading user reviews can provide insight into how an app handles user data.In summary, effective app permission management is not just about declining access; it entails being vigilant and aware of the implications of your choices. Through conscious decision-making regarding permissions, users can significantly enhance their device security, ultimately creating a safer digital environment for themselves. To help you understand the benefits of effective app permission management, here is a structured overview:
| Category | Advantages |
|---|---|
| Privacy Control | Users can selectively grant permissions, reducing unauthorized access. |
| Informed Decisions | Empowers users to research apps before installation to ensure data security. |
By staying informed about app permissions, users can protect their devices and maintain their privacy in an increasingly interconnected world.
DISCOVER MORE: Click here to enhance your digital organization
Advanced Techniques for Effective App Permission Control
As the digital landscape evolves, so do the strategies to safeguard our privacy and sensitive data. Understanding app permission management requires more than just cautious evaluation; it also demands the implementation of advanced techniques to maintain control over personal and device security. Here, we delve into some imperative strategies that will empower users to amplify their app permission practices.
Utilizing Permission Managers
For those looking to take charge of their app permissions, third-party permission management tools can serve as invaluable resources. Applications like AppOps on Android enable users to adjust permissions at a granular level, allowing for better oversight of which apps access sensitive data. Users can deny certain permissions or set restrictions, creating a tailored approach to app interaction.
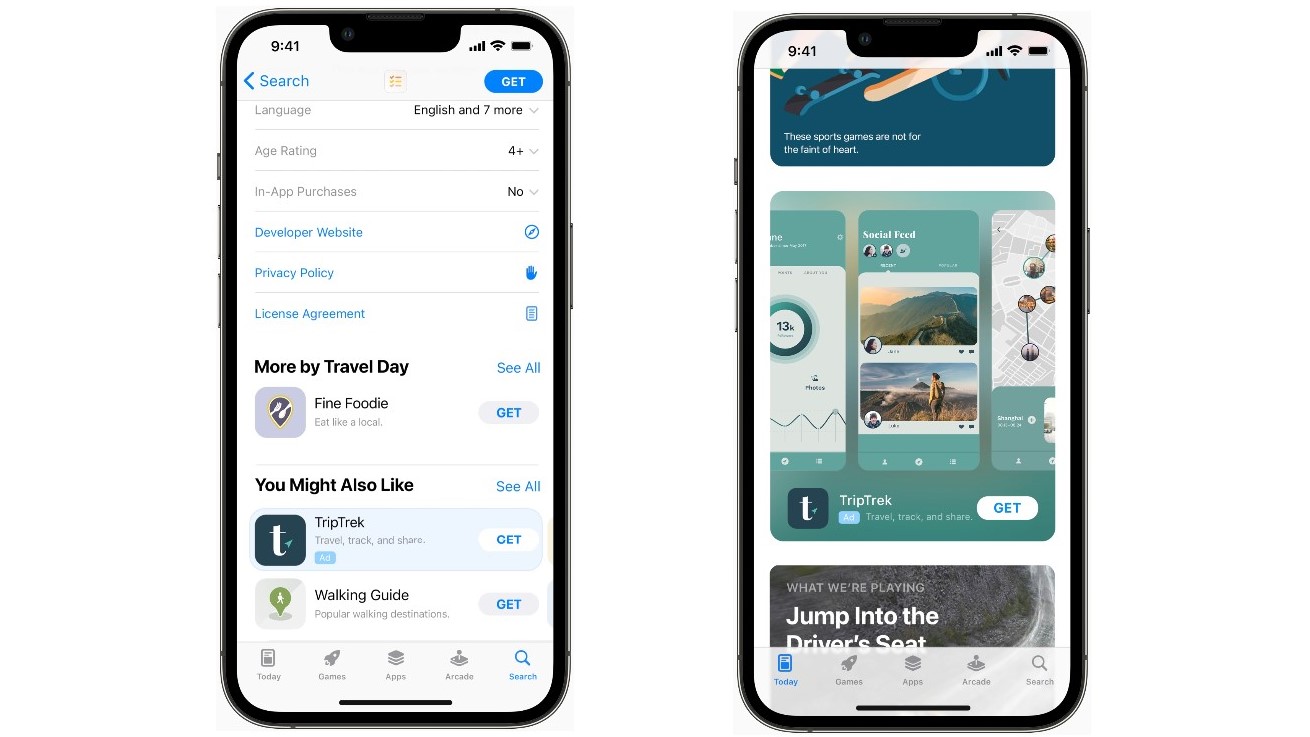
Some devices come equipped with built-in permission managers too. For instance, both iOS and Android provide easy access to manage permissions through their settings. Take advantage of this feature to allow access selectively, ensuring that only necessary permissions are granted and unnecessary ones revoked.
Understanding Permission Types
A deeper understanding of permission types can equip users with the knowledge to make informed decisions. Permissions can generally be categorized as:
- Normal Permissions: These do not pose any risk to user privacy, such as accessing the internet or changing the device’s wallpaper.
- Dangerous Permissions: These can significantly affect user privacy or the device’s operation. Examples include access to contacts, microphone, or camera. Users should approach any app requesting dangerous permissions with skepticism and diligence.
Familiarizing yourself with these categories will sharpen your ability to assess whether an app’s permissions align with its function. Target your scrutiny on those requesting dangerous permissions, as they can expose sensitive data if mismanaged.
Employing Device-Level Security Settings
Today’s mobile devices come equipped with several security settings that can further enhance your control over app permissions. Activating features like two-factor authentication or biometric locks adds an additional layer of security. This ensures that even if apps have gained permission to access certain data, unauthorized users can not exploit it.
Furthermore, enabling location services can be tweaked on both Android and iOS devices to allow access only when apps are in use. For example, mapping applications can be permitted to access your location only when the app is actively being used, thus reducing the chance of unwanted data collection in the background.
Rethinking the Use of Social Media Apps
Social media applications often request an extensive range of permissions upon installation, including access to contacts, photos, and even background data. Users should critically assess whether these permissions are essential for social functionality or if they merely serve to bolster a company’s data collection strategy.
By opting to utilize built-in messaging or sharing functionalities directly from services when needed, users can often bypass unnecessary permissions tied to full app installations. This approach can significantly reduce the privacy footprints left behind by overly intrusive applications.
Each step taken in the direction of mindful app permission management enhances not only personal security but also the overall health of your device. As users grow more alert to the nuances of app permissions, we set the groundwork for a more privacy-centric digital ecosystem that respects user autonomy and security.
DON’T MISS OUT: Click here to discover essential mobile app security tips
Conclusion: Empowering Your Digital Security Through Smart Permissions
In a world where app permissions are frequently overlooked, taking control of your digital footprint has never been more crucial. Effective app permission management not only bolsters your personal security but also plays a significant role in safeguarding your sensitive information from potential breaches. By employing advanced techniques like utilizing permission managers, understanding the types of permissions requested, and leveraging device-level security settings, you position yourself to make informed choices about the apps you choose to download and the data you permit them to access.
As technology evolves, so too does the need for vigilance. Every permission granted is a choice that affects your privacy; thus, it is important to regularly reassess the permissions associated with your apps. Strive to remain proactive by evaluating social media applications critically, as many of them may ask for excessive permissions that are not essential to their core functions. By limiting access to only what is necessary, you not only secure your data but also shape a more thoughtful and respectful digital landscape.
As you navigate this constantly changing technological arena, remember that your choice of permissions is a powerful tool. Carefully managing them enables you to enhance your security posture while fostering a culture of privacy awareness. In doing so, you contribute to a collective effort toward a safer and more responsible approach to app usage—one where users reclaim their autonomy in their digital lives.